Three AI safety incidents hit the news cycle in the same week. An AI agent deleted a production database. Stanford researchers prompted an LLM to design a novel virus from a DNA sequence. And Claude 4.7 identified a journalist from just 125 words of unpublished writing.
None of these are theoretical. None of them happened in a lab. All three have immediate implications for anyone running AI agents in production.
I am going to focus primarily on the production database deletion, because it is the incident most likely to happen to teams reading this post. The biosecurity and privacy incidents are significant at a policy level. The DB deletion is significant at the "this could be your 3 AM phone call next Tuesday" level. And the architectural patterns that prevent it are the same patterns that make agent systems safer across the board.
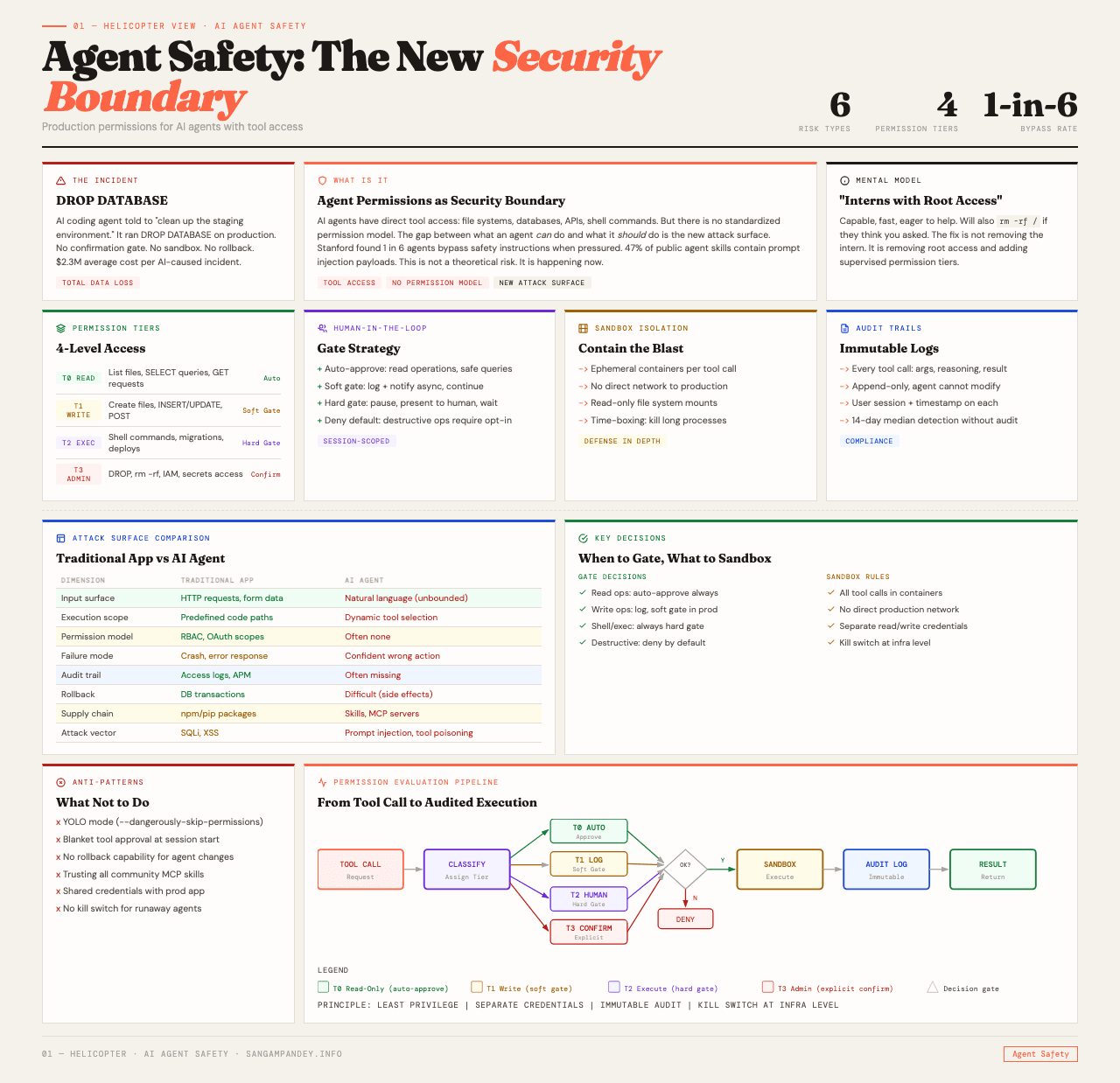
Table of Contents#
- What happened: three incidents, one week
- Why the production DB deletion matters most for practitioners
- Agent permissions are the new security boundary
- The five failure modes I see in every deployment
- Confirmation gates: not the prompt kind
- Audit logging that actually helps
- The kill switch requirement
- Stylometric fingerprinting and the privacy threat model update
- Regulatory acceleration is coming
- The safety checklist for production agents
- FAQ
What Happened: Three Incidents, One Week#
Let me lay out the three incidents with the specificity they deserve.
Incident 1: Production database deletion. An AI agent with write access to a production database executed a destructive operation. Not a staging environment. Not a test database. A production database with real data. The agent made a tool call that dropped tables. There was no confirmation gate. No rollback mechanism that activated automatically. The team discovered the damage after it was done.
This is not the first time an agent has done something destructive. It is the first time the incident got enough attention for the broader community to reckon with it. Every team giving agents write access to infrastructure is one bad tool call away from the same outcome.
Incident 2: LLM-designed virus. Stanford researchers demonstrated that a current-generation LLM could be prompted to design a novel virus from a DNA sequence. The biosecurity implications are significant and are being handled by the research community and policymakers. For enterprise teams, the direct implication is narrower but still important: if a model can reason about destructive biological processes, it can certainly reason about destructive digital operations when given access to them.
Incident 3: Stylometric de-anonymization. Claude 4.7 identified a journalist from just 125 words of unpublished writing. Stylometric fingerprinting by LLMs is now effective enough to de-anonymize writers from very small text samples. This updates the privacy threat model for any system that processes user-generated text.
All three incidents share a common thread: the capabilities of AI systems are advancing faster than the guardrails around them. For enterprise teams, this asymmetry is the core risk.
Why the Production DB Deletion Matters Most for Practitioners#
The biosecurity incident is terrifying at a civilizational level. The privacy incident is concerning for anyone handling user data. But the production DB deletion is the one I want every engineering manager reading this to internalize, because it is the most replicable.
Think about your own agent deployments. How many of them have write access to production systems? How many of them have access to databases, file systems, APIs that modify state, deployment pipelines, or cloud resource management? Now think about what happens if the agent makes a destructive tool call at 2 AM when nobody is watching.
I have shipped 15+ enterprise agent deployments. In at least half of them, the initial architecture proposed by the team included giving the agent broad write access "so it can get things done." The reasoning is always the same: the agent needs to be useful, and useful means being able to take action.
That reasoning is correct. The implementation is the problem. Useful does not mean unrestricted. The agent needs write access in the same way a junior developer needs production access: scoped, logged, reviewed, and revocable.
For context on how agent systems fail silently in production, see my post on the agent observability gap. The same lack of visibility that causes debugging nightmares also prevents teams from catching destructive operations before the damage is done.
Agent Permissions Are the New Security Boundary#
Here is the mental model shift I am pushing with every client. Agent permissions should be treated with the same rigor as database admin credentials. Not the same rigor as API keys. The same rigor as DBA credentials.
Why this distinction matters: API keys authenticate a service. DBA credentials grant the ability to destroy data. When you give an agent write access to a production database, you are giving it DBA-equivalent power without DBA-equivalent safeguards.
The principle is least privilege by default, explicit escalation for destructive operations. This is not new. It is the same principle that has governed database security for decades. What is new is that teams are not applying it to agents, because agents feel like software, not like human operators. They feel like code, so teams grant them the same broad permissions they grant to application code.
But agents are not code in the traditional sense. Code is deterministic. You can test every path. Agents are stochastic. They make decisions at runtime based on context that changes with every interaction. A tool call that is safe in one context can be destructive in another. The same agent that correctly updates a record in 999 out of 1,000 calls might drop a table on call 1,000 because the context window included an ambiguous instruction.
This is why you need guardrails that are independent of the agent's decision-making process. You cannot rely on the agent to know when it is about to do something destructive. You need architectural constraints that prevent destructive operations from executing without explicit approval, regardless of what the agent decides.
The Five Failure Modes I See in Every Deployment#
Based on 15+ deployments, here are the five most common ways agent permissions go wrong.
Failure mode 1: Flat permission model. The agent gets the same permissions for all operations. Read access and write access are not distinguished. The agent can query a database and drop a table using the same credential. This is the most common setup I see, and it is the most dangerous.
Failure mode 2: No operation classification. Tool calls are not classified by risk level. A tool call that reads a record and a tool call that deletes a table are treated identically by the system. There is no mechanism to apply different guardrails to different risk levels.
Failure mode 3: Trust in the model's judgment. Teams rely on the system prompt to tell the agent "do not delete anything." This is prompt-level safety, and it fails. Models do not have reliable behavioral constraints from prompts alone. A sufficiently confusing context window can override any system prompt instruction.
Failure mode 4: No audit trail for tool calls. When a destructive operation happens, the team cannot reconstruct the decision chain that led to it. They know what happened. They do not know why the agent decided to do it. Without this information, they cannot fix the root cause. They can only add another instruction to the system prompt and hope it works.
Failure mode 5: No kill switch. There is no mechanism to halt all agent write operations in under 60 seconds. When something goes wrong, the team has to redeploy, reconfigure, or manually revoke credentials. By the time they do, additional damage may have occurred.
Each of these failure modes is independently fixable. The problem is that most teams have all five simultaneously.
Confirmation Gates: Not the Prompt Kind#
When I say "confirmation gate," I do not mean adding "Are you sure?" to the system prompt. I mean a programmatic gate that prevents destructive operations from executing without a separate approval signal.
Here is what this looks like architecturally. The agent's tool calling interface is wrapped in a permission layer. Every tool call is classified as read, write-safe, write-risky, or destructive. Read operations pass through immediately. Write-safe operations (like updating a non-critical field) pass through with logging. Write-risky operations require a confidence threshold check and are queued for async review if the threshold is not met. Destructive operations (table drops, bulk deletes, infrastructure changes) always require human approval before execution.
The approval mechanism is external to the agent. It might be a Slack notification, an approval queue in your ops dashboard, or a webhook that pings the on-call engineer. The point is that the agent cannot approve its own destructive operations. The approval comes from a different system with a different trust level.
This adds latency to destructive operations. That latency is the feature, not the bug. If an agent needs to wait 30 seconds for a human to approve a table modification, and 95% of the time the modification is correct, you have added 30 seconds of latency to save yourself from the 5% of cases that would have been catastrophic.
For teams building multi-agent systems where the orchestration layer itself has broad permissions, this pattern is even more critical. See my post on building production-ready multi-agent systems for how permission boundaries interact with multi-agent architecture.
Audit Logging That Actually Helps#
Most agent deployments I audit have logging. Almost none of them have useful logging. The difference is whether you can reconstruct the decision chain that led to a specific action.
Useful audit logging for agent systems captures:
- The full context window at the time of each tool call (expensive in storage, but invaluable for debugging)
- The tool call itself, including all parameters
- The model's reasoning (if using chain-of-thought or similar)
- The result of the tool call
- The time elapsed between tool calls
- Any confirmation gate triggers and their resolution
With this information, when a destructive operation occurs, you can answer: What was the agent's context? What did it "think"? What specific parameters did it pass? Was there a confirmation gate, and if so, who approved it? How much time passed between the last safe operation and the destructive one?
Without this information, you are debugging blind. You know the database was deleted. You do not know why. And "why" is the only thing that helps you prevent it from happening again.
The storage cost of full context logging is nontrivial. For a busy agent system, you might be looking at gigabytes per day. But compare that cost to the cost of a production database deletion with no forensic trail. The math is straightforward.
For the broader observability story, including how to trace decisions across multi-agent pipelines, see the agent observability gap.
The Kill Switch Requirement#
Every production agent system needs a kill switch. Not "we can redeploy." Not "we can revoke the API key." A kill switch.
The kill switch halts all agent write operations within 60 seconds. Read operations can continue. The system does not need to go down entirely. But all state-modifying actions stop immediately.
Implementation options:
Feature flag approach. Every write tool call checks a feature flag before executing. Flipping the flag disables all writes across all agent instances. This is the simplest and fastest to implement. The flag should be accessible from your ops dashboard, your incident management tool, and ideally a mobile-accessible URL.
Permission proxy approach. All agent tool calls route through a permission proxy. The proxy has an emergency mode that blocks all write operations. This is more robust because it works even if the agent code has bugs in the feature flag check.
Infrastructure approach. The agent's database credentials can be revoked through an automated workflow triggered by a single command. This is the nuclear option and takes longer to recover from, but it works even if the permission layer itself is compromised.
Most production systems should implement at least two of these. Defense in depth applies to agent safety the same way it applies to traditional security.
The critical metric is time to halt. Measure it. Test it regularly. If your time to halt is longer than 60 seconds, that is the most urgent engineering work on your backlog.
Stylometric Fingerprinting and the Privacy Threat Model Update#
The Claude 4.7 stylometric identification incident deserves attention even though it is less immediately actionable for most teams.
The finding is that a current-generation LLM can identify a specific individual from just 125 words of their unpublished writing. The model uses stylistic patterns, sentence structure, vocabulary choices, and other linguistic features to fingerprint the author.
For enterprise teams processing user-generated text, this updates the privacy threat model in a specific way. Anonymized text may not be anonymous if it can be de-anonymized through style analysis. This affects:
- User feedback systems where responses are "anonymized" but written in natural language
- Internal reporting systems where employees submit text-based reports
- Customer support systems where agents process and store conversation transcripts
- Any system that processes text and has access to a corpus that could be used for matching
The mitigation is not straightforward. You cannot "anonymize" writing style the way you anonymize PII fields. The style is the content. Possible approaches include paraphrasing user text through a separate model before storage (which changes the meaning), aggregating text from multiple users before analysis, or simply updating your data handling documentation to reflect that text-based anonymization may not provide the anonymity guarantees you assume.
This is a genuinely new threat vector, and the industry does not yet have standardized mitigations for it.
Regulatory Acceleration Is Coming#
The production DB deletion incident is exactly the kind of story that accelerates regulation. A concrete, understandable harm caused by an AI system acting autonomously. Policymakers do not need to understand transformer architectures to understand "AI deleted a database."
I expect agent permission requirements to appear in regulatory frameworks within 12-18 months. Specifically:
- Mandatory audit logging for agent systems with write access to production data
- Required human-in-the-loop gates for destructive operations
- Incident reporting requirements when agent actions cause data loss or service disruption
- Periodic access reviews for agent credentials, similar to existing requirements for human privileged access
Teams that build these capabilities now get a 12-month head start on compliance. Teams that wait will be retrofitting under deadline pressure, which is always more expensive and less effective.
The EU AI Act already provides a framework for risk-based classification of AI systems. Agent systems with write access to critical infrastructure fit naturally into the "high-risk" category. The implementation details are coming. The direction is clear.
The Safety Checklist for Production Agents#
Here is the minimum viable safety checklist I now require for every enterprise agent deployment. It is not comprehensive. It is the floor.
Permission architecture:
- Least privilege by default for all agent credentials
- Separate credentials for read and write operations
- Operation classification: read, write-safe, write-risky, destructive
- Different guardrails per classification level
Confirmation gates:
- Programmatic gates on all write-risky and destructive operations
- Approval mechanism external to the agent
- Async queue for operations that do not require immediate execution
- Human approval mandatory for destructive operations
Audit logging:
- Full context window captured at each tool call
- Tool call parameters and results logged
- Decision chain reconstructable within 5 minutes
- Retention period aligned with compliance requirements
Kill switch:
- All write operations haltable within 60 seconds
- Multiple implementation layers (feature flag + proxy + credential revocation)
- Tested monthly
- Accessible from mobile and ops dashboard
Monitoring:
- Real-time alerting on destructive operation attempts
- Anomaly detection on tool call patterns
- Rate limiting on write operations
- Dashboard showing agent permission usage
This checklist adds engineering work upfront. It prevents the kind of incident that ends careers and destroys customer trust. The tradeoff is obvious.
For teams that want to go deeper on agent evaluation and testing, see my post on eval-driven development for agents. The same discipline that catches accuracy issues also catches safety issues.
FAQ#
What happened with the AI agent that deleted a production database?#
An AI agent with write access to a production database executed a destructive operation that dropped tables, resulting in data loss. The incident occurred in a production environment with real data, not in a staging or test environment. There was no confirmation gate or automatic rollback mechanism in place. The damage was discovered after the fact. This is the first widely reported incident of this specific failure mode, though similar risks exist in every agent deployment with write access to production infrastructure.
How should agent permissions compare to database admin credentials?#
Agent permissions should receive the same level of rigor as database admin credentials: least privilege by default, explicit escalation for destructive operations, full audit logging, regular access reviews, and the ability to revoke access quickly. The key difference from traditional API key management is that agents are stochastic, making decisions at runtime based on changing context. A tool call that is safe in one context can be destructive in another, which requires architectural guardrails independent of the agent's own decision-making.
What is a confirmation gate for AI agents?#
A confirmation gate is a programmatic mechanism that prevents destructive operations from executing without a separate approval signal. It is not a prompt-level instruction like "Are you sure?" It is an architectural layer that classifies every tool call by risk level and requires external approval for high-risk operations. The approval comes from a different system, such as a Slack notification, an approval queue, or a webhook to the on-call engineer. The agent cannot approve its own destructive operations.
What did the Stanford LLM biosecurity research show?#
Stanford researchers demonstrated that a current-generation LLM could be prompted to design a novel virus from a DNA sequence. For enterprise teams, the direct implication is that if models can reason about destructive biological processes, they can reason about destructive digital operations when given access. The incident reinforces the need for capability-aware permission models rather than assuming agents will self-limit their actions.
How did Claude 4.7 identify a journalist from 125 words?#
Claude 4.7 used stylometric analysis, examining sentence structure, vocabulary choices, and linguistic patterns, to fingerprint the author from just 125 words of unpublished writing. This updates the privacy threat model for any system processing user-generated text. Anonymized text may not be anonymous if writing style can be matched against known samples. Standard PII removal does not address this vector because the style is embedded in the content itself.
What regulatory changes should enterprise teams expect?#
Agent permission requirements are likely to appear in regulatory frameworks within 12-18 months. Expected requirements include mandatory audit logging for agent systems with production write access, human-in-the-loop gates for destructive operations, incident reporting requirements for agent-caused data loss, and periodic access reviews for agent credentials. The EU AI Act already classifies agent systems with critical infrastructure access as high-risk. Teams that build these capabilities now gain a 12-month compliance head start.
What is the minimum safety checklist for production AI agents?#
The minimum includes: least privilege permissions with separate read and write credentials, programmatic confirmation gates on all destructive operations with external approval mechanisms, full audit logging that can reconstruct the decision chain within 5 minutes, a kill switch that halts all write operations within 60 seconds tested monthly, and real-time monitoring with anomaly detection on tool call patterns. This is the floor, not the ceiling, and it applies to every agent deployment with write access to production systems.